Using Active Directory Accounts
MSP360 Managed Backup suggests using the Active Directory(AD) Bridge tool that comes as a specialized gateway solution developed to simplify cloud storage deployment in large corporate networks. It allows authenticating Windows domain users as Managed Backup users. End users log onto their Windows computers and start using Managed Backup without specifying their domain credentials, so some security advantages are added to the authentication. To manage Active Directory accounts, the *Miscellaneous > Active Directory server permission should be granted as the administrator permission on Organization > Administrators.
AD Bridge Licensing
No license is required. AD Bridge is available free of charge.
This chapter covers the following topics:
- AD Bridge Installation and Configuration
- Enable AD Authentication for Backup Agent
- Use Backup Agent with AD Bridge
System Requirements
Computer for the AD Bridge tool must have Microsoft .Net 4.0 or later installed.
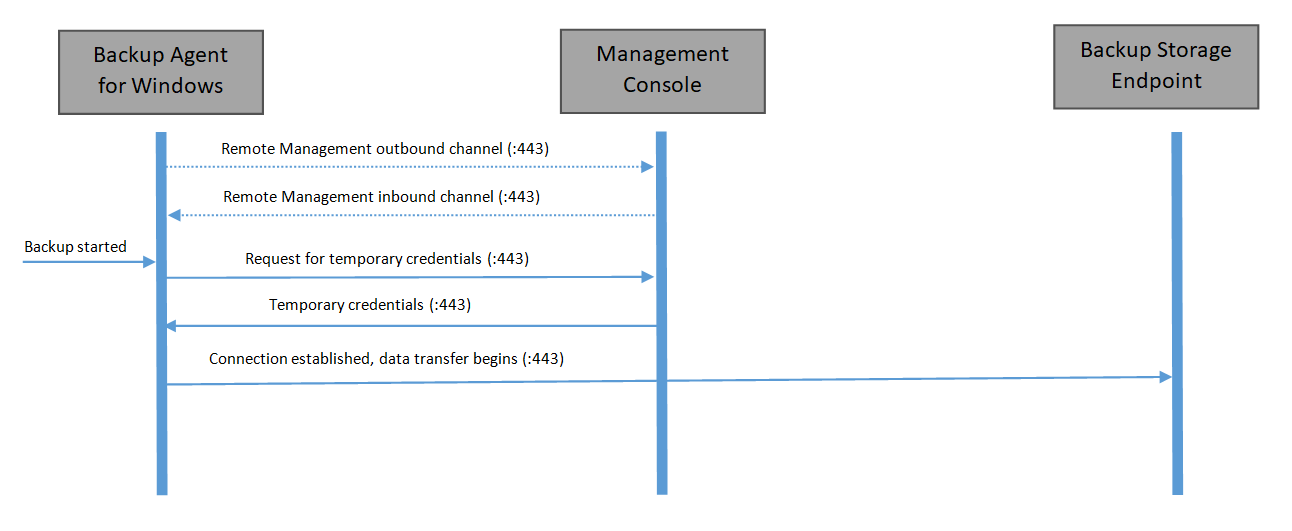
How AD Bridge Works
Backup process communication workflow is the following:
Installation and Configuration
- Download AD Bridge installation package here
- Install the downloaded installation package on one of the domain computers.
- Once the installation is completed, run the application.
- Specify AD Bridge settings.
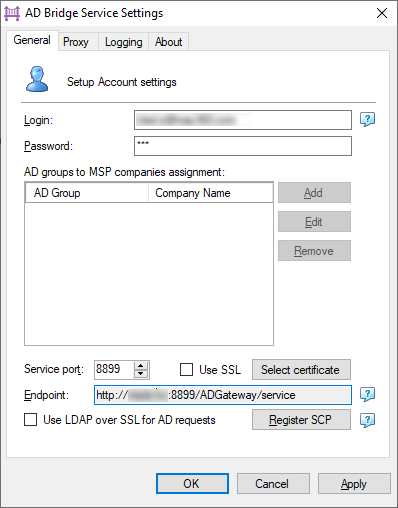
On the General tab, specify your Managed Backup provider credentials:
- Login. Your Managed Backup provider email or email of an administrator with the "Active Directory Server" permission enabled
- Password. Managed backup password of specified account. Press Tab to retrieve a list the companies for AD Bridge. Add buttin become active when the listing is finished.
Select the AD groups to link to Managed Backup. To manage AD groups, use the Add, Edit, and Remove buttons.

- Service Port. Specify the service port number
- Use SSL. Select this check box to use the SSL protocol, then upload the SSL certificate
- In the Endpoint field, specify the URL for configuring MBS users
- Use LDAP over SSL for AD requests. Sometimes network security policy requires this protocol. Select this check box to enable it for AD requests
- Register SCP. Register a Service Connect Point in Active Directory for AD Bridge (optional). So that MBS Agents will automatically detect the AD Bridge endpoint.
Note: registering SCP requires master permissions to the Active Directory
- Once you are done, click OK or Apply.
- Click OK to apply settings.
| Top |
Enable Authentication for Backup Agent
Before using Backup Agent with the Active Directory authentication, enable the appropriate option in the Management Console.
- Open the Management Console.
- In the Settings menu, select Global Agent Options.
- In the Authentication group, select Show Windows Authentication (AD Bridge) option check box.
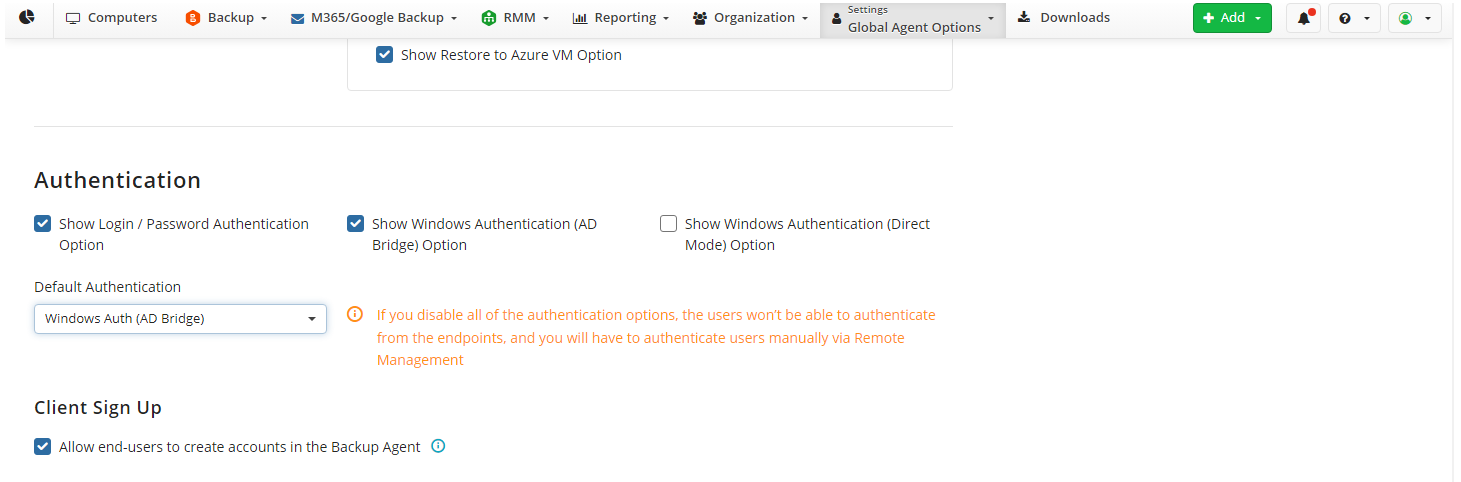
- In the Default Authentication drop-down list, select the required authentication method (Windows auth (AD Bridge), for example).
- Once you are done, click Save Changes.
| Top |
Using Backup Agent with AD Bridge
To start using AD authentication, proceed as follows:
- Install the Backup Agent instance on a customer's domain computer.
- Select the "Use Windows authentication (AD Bridge)" option:
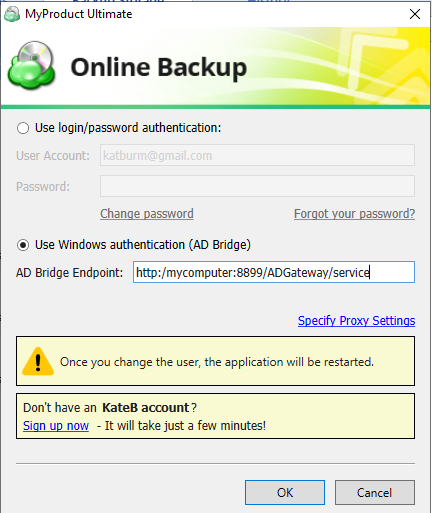
You may need to enter the AD Bridge endpoint manually if it was not registered in Active Directory using "Register SCP" during AD Bridge configuration.
- Click OK.
Alternatively, you can auto-configure the installation and authentication process if you deploy the following script via Windows GPO:
net use s: \\dc\share
mkdir c:\backup
cd c:\backup
powershell -Command "Invoke-WebRequest http://s3.amazonaws.com/yourBuildURL.exe -OutFile cbl.exe"
cbl.exe /S /autoregadbridge="http://ADBRIDGE-PC:8900/ADGateway/Service/"
Make sure all arguments specified in the script are relevant.
Once the Backup Agent is configured, a corresponding Managed Backup user is automatically created. Managed Backup user name is the name of a customer's domain account.
| Top |