Support for Single Sign-On
Management Console supports Google Workspace and Microsoft Entra ID (formerly Azure AD) Single Sign-On. The support for Single Sign-On unburdens users from having to memorize credentials for different apps or reusing weak passwords, increasing the risk of a data breach.
About Single Sign-On
Single Sign-On is an authentication method that allows users to sign in using one set of credentials to multiple independent software systems.
Using SSO means a user doesn't have to sign in to every application they use. With SSO, users can access all needed applications without being required to authenticate using different credentials.
Prepare Management Console for SSO
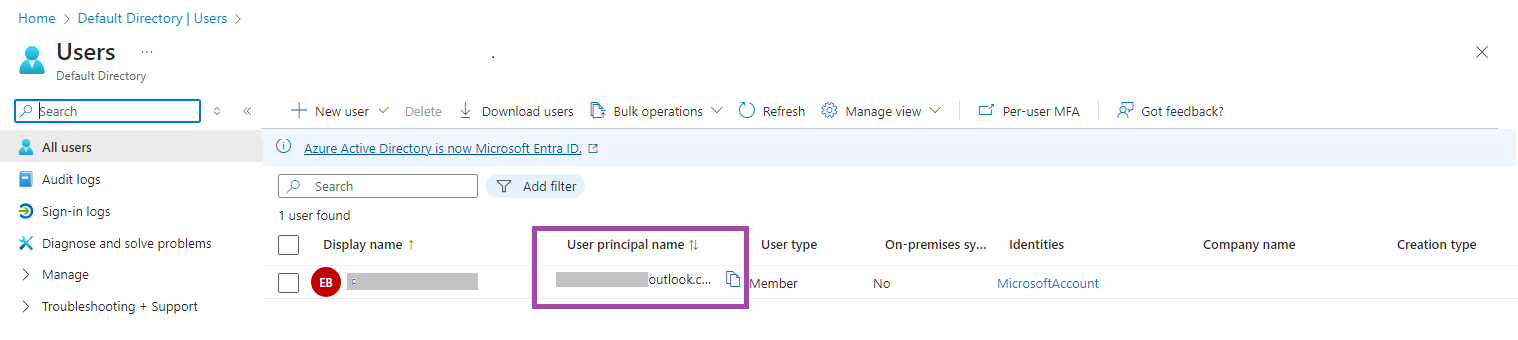
- Create an administrator account on Organization > Administrators with the user principal name of your Microsoft Entra ID / Google Workspace user. You can create a separate user for this purpose.
You should use the user principal name only for SSO (Microsoft). All other email addresses associated with the Microsoft Entra ID user do not work for this purpose.
- There are no mandatory permissions for this administrative account to use SSO. You can grant this account only the permissions you need for other tasks, e.g., to use the associated Azure storage account.
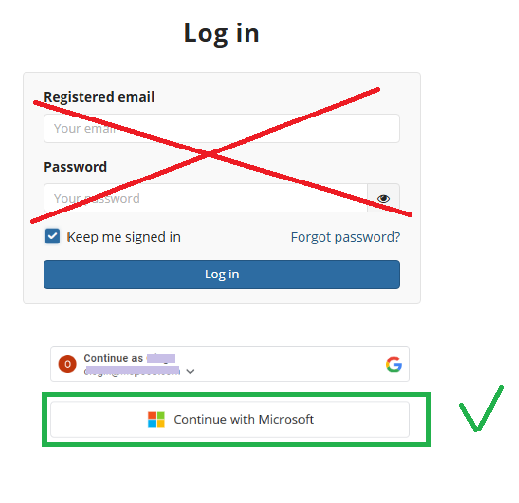
Log in Using Microsoft
To log into Management Console using your Microsoft Entra ID (formerly Azure AD) credentials account, click the Microsoft button below the login and password fields and proceed with Microsoft Authentication using your Microsoft Entra ID account credentials.
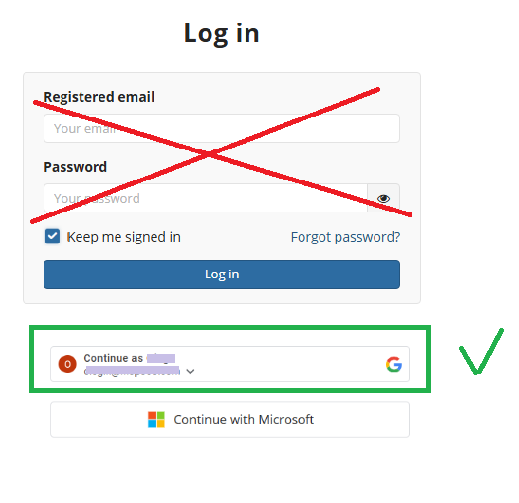
Log in Using Google
To log into Management Console using your Google Workspace account, click the Google button below the login and password fields and proceed with Google Authentication using your Google Workspace account credentials.
| Top |